ShinyHunters Claims 280 Million Records Stolen from Instructure's Canvas Platform
Extortion group ShinyHunters targets education technology giant, escalating risks for institutions and students.

UNITED KINGDOM —
Key facts
- ShinyHunters claims to have stolen 280 million data records from Instructure's Canvas platform.
- The stolen data reportedly affects 8,809 colleges, school districts, and online education platforms.
- Instructure confirmed a cyber incident and subsequent data breach affecting its cloud-hosted environment.
- The hackers demanded payment from Instructure by May 6, 2026, threatening to leak data.
- Affected data includes user names, email addresses, and private messages.
- More than 40 percent of colleges and universities use Canvas.
- ShinyHunters has previously targeted educational technology vendors like Salesforce and Infinite Campus.
Cyberattack Exposes Millions of Education Records
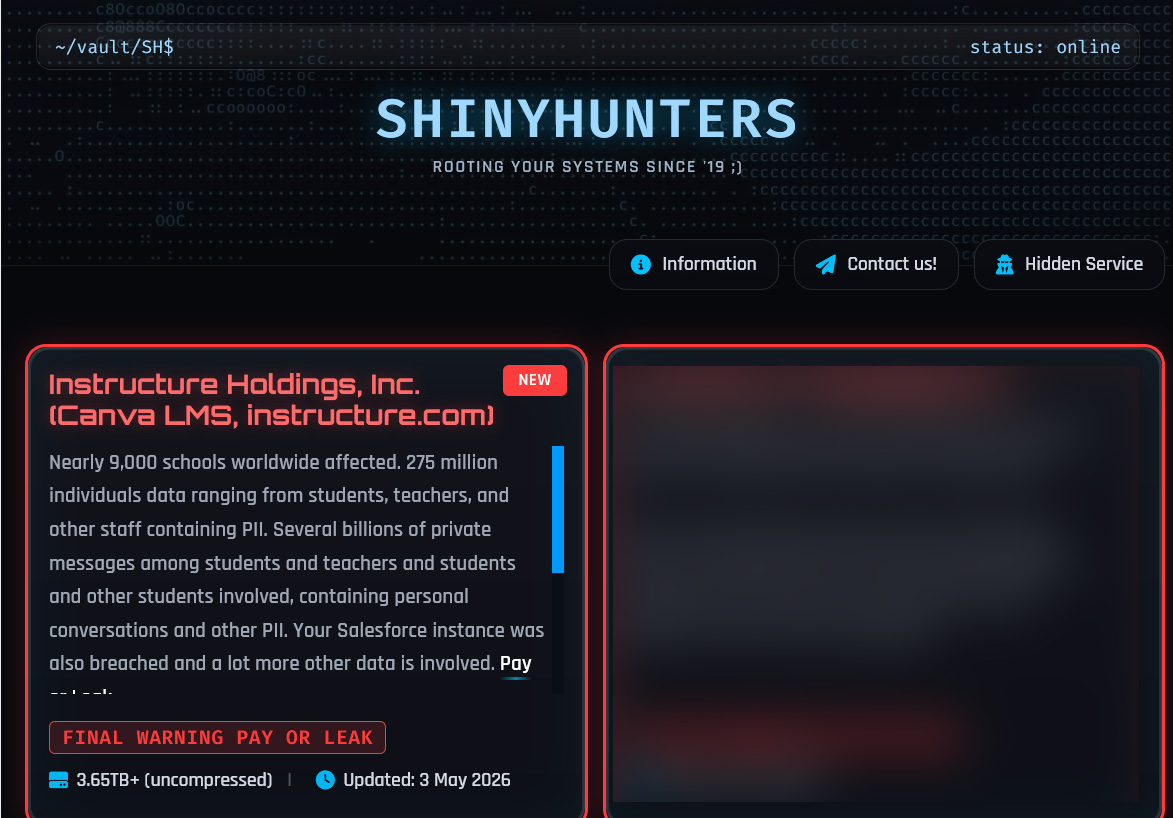
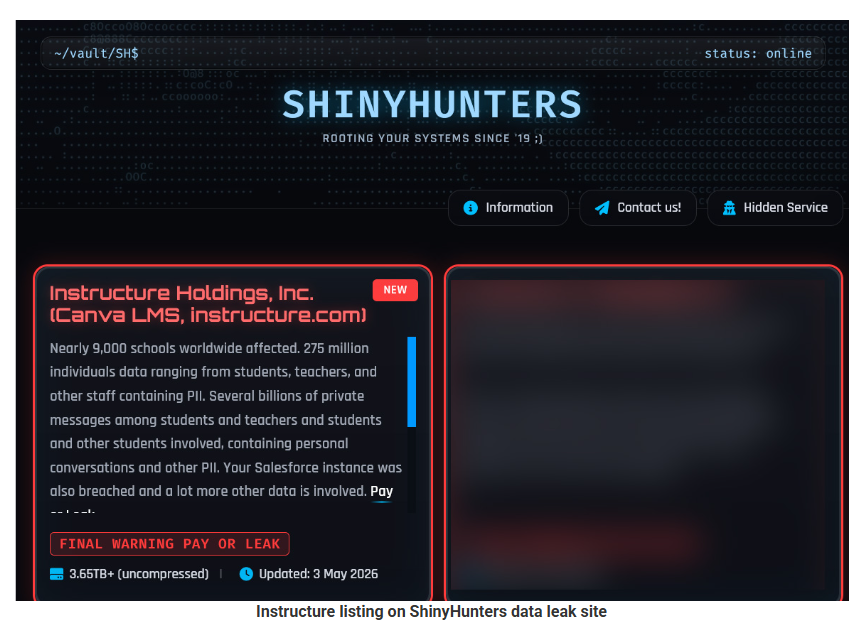
The criminal extortion group ShinyHunters has claimed responsibility for a significant data breach at Instructure, the company behind the widely used Canvas learning management system. The hackers assert they have exfiltrated 280 million records pertaining to students, teachers, and staff from a vast network of educational institutions. This incident serves as a stark reminder of the escalating threat posed by cybercriminals targeting third-party vendors in the education sector. Instructure, which provides the Canvas platform used by more than 40 percent of colleges and universities, confirmed a cyber incident affecting its cloud-hosted environment. While the company has stated it is investigating the breach with external forensics experts, the ramifications for the millions of individuals whose data may have been compromised are considerable. The attackers have issued a ransom demand, setting a deadline of May 6, 2026, for Instructure to comply or face a public leak of the stolen information. This ultimatum underscores the aggressive tactics employed by groups like ShinyHunters, who see significant value in compromising large educational technology providers.
The Scope of the Alleged Data Theft
ShinyHunters has published a list of 8,809 school districts, universities, and online education platforms that they claim were impacted by the breach. The group provided record counts for each institution, with figures ranging from tens of thousands to several million per entity. The exact nature of the compromised data, according to the hackers, includes user names, email addresses, and private messages exchanged within the Canvas system. While Instructure has not publicly detailed the full extent of the breach, a sample of stolen data viewed by one news outlet reportedly contained names, email addresses, and some phone numbers, but notably excluded passwords. The company has indicated that certain types of data were unaffected. This incident highlights a growing trend where cybercriminals bypass individual institutions to target the vendors that serve them. By compromising a single vendor like Instructure, attackers can gain access to data from a multitude of downstream clients, amplifying the potential impact.
ShinyHunters' History of Education Sector Attacks
The ShinyHunters group is no stranger to targeting the education technology landscape. This latest alleged breach follows a pattern of high-profile attacks on companies serving academic institutions. Last fall, hackers linked to ShinyHunters claimed to have stolen approximately one billion customer records from Salesforce, impacting dozens of companies, including Instructure itself. In March, the group infiltrated Infinite Campus, a student information system widely used in K–12 education. More recently, in April, ShinyHunters took credit for accessing internal data at the publisher McGraw Hill. These repeated incursions demonstrate a strategic focus on the education sector, where vast amounts of sensitive personal data are stored. Experts suggest that this focus stems from the rich data available within educational platforms, which can be leveraged for highly personalized phishing attacks. The ability to reference real courses and conversations makes these subsequent attacks far more convincing and successful.
Instructure's Response and System Status
Following the confirmation of the cyber incident, Instructure's Chief Information Security Officer, Steve Proud, provided updates on the company's status. Proud confirmed that the breach was perpetrated by a criminal threat actor and that the company was actively investigating with the assistance of outside forensics experts. He assured that any impacted institutions would be notified if the situation changed. As of Monday, its Canvas Data 2 and Beta services should be available to all customers. However, another version of the learning management system, Canvas Test, remained under maintenance. The company has not yet responded to specific questions regarding the ransom demand. The incident has prompted some universities to issue statements to their communities. The University of Colorado Boulder acknowledged awareness of the breach involving Instructure, describing it as a nationwide event affecting multiple institutions. Rutgers University stated it had not been notified of any direct impact and that Canvas remained operational for its users, while Tilburg University indicated an investigation was underway to determine the extent of any data compromise.
The Increased Value of Vendor Breaches
The attack on Instructure underscores the significant value cyberattackers derive from targeting third-party vendors rather than individual organizations. As one expert noted, it is akin to a bank robber discovering where the armored trucks make their stops. The risk is now amplified downstream, as a single breach can compromise data across numerous institutions. This approach allows attackers to cast a wider net and potentially access more comprehensive datasets. The data stolen from Instructure, including names, email addresses, and messages, can be used to craft highly targeted and convincing phishing campaigns. These attacks, which can reference specific courses or communications, are significantly more likely to succeed than generic scams. "Even organizations that do the right things can still be exposed through trusted vendors," an expert observed. This situation calls for a systemic approach to cybersecurity, emphasizing stronger defenses, greater supply-chain accountability, and a recognition that data breaches are not isolated events but part of a broader strategic threat landscape.
Guidance for Parents and Students
In the wake of the Instructure breach, parents and students are advised to take proactive steps to protect their personal information. It is crucial to first verify the authenticity of any notifications received from schools or Instructure, being wary of suspicious links or urgent requests for data. Direct verification through official channels is recommended. For any Canvas or related accounts, changing passwords immediately is paramount, especially if schools allow direct username and password logins. It is advisable to use unique, strong passwords for every account and consider using a password manager. Enabling multi-factor authentication (MFA) wherever possible adds a critical layer of security. Parents should also remind children never to share security codes, as these act as short-term passwords. If the breach involved highly sensitive identifiers, such as national ID or Social Security numbers, inquiries should be made to both the school and the provider regarding protection services like credit monitoring or identity restoration. Even for young children without credit files, noting this incident is important for future record checks.
The bottom line
- The ShinyHunters group claims to have stolen 280 million records from Instructure's Canvas platform, impacting 8,809 educational institutions.
- Instructure has confirmed a cyber incident and data breach affecting its cloud-hosted environment, with user names, email addresses, and messages reportedly compromised.
- The attackers have issued a ransom demand to Instructure with a deadline of May 6, 2026.
- ShinyHunters has a history of targeting educational technology vendors, including Salesforce and Infinite Campus.
- The breach highlights the increased risk associated with third-party vendors in the cybersecurity landscape.
- Institutions and individuals are advised to enhance security measures, including password management and multi-factor authentication.





UK Proposes Rule Changes to Shield Summer Flights from Fuel Woes

Palace Pursue European Glory Amidst Glasner's Farewell Tour

UK Pensioners Urged to Claim Up to £114 Weekly Benefit
