Bluekit Phishing Kit Offers 40+ Templates and AI Assistant for Automated Campaigns
A new all-in-one platform lets cybercriminals draft phishing emails using models like GPT-4.1 and Claude, while a separate DHL-themed kit uses OTP lures and EmailJS to steal credentials.

PHILIPPINES —
Key facts
- Bluekit includes over 40 templates targeting services such as Gmail, Outlook, iCloud, GitHub, and Ledger.
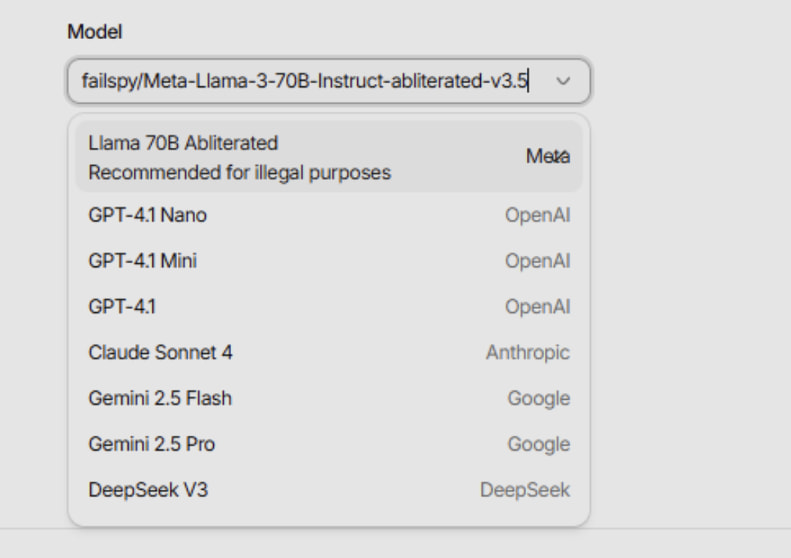
- The kit's AI Assistant supports Llama, GPT-4.1, Claude, Gemini, and DeepSeek to draft phishing emails.
- Varonis analyzed a limited version of Bluekit and found placeholder content, indicating early-stage development.
- Bluekit integrates domain purchase, phishing page setup, and campaign management into a single panel.
- Stolen data is exfiltrated via Telegram private channels.
- A separate DHL phishing kit uses a fake OTP page and branded login portal, exfiltrating data via EmailJS.
- Forcepoint X-Labs analyzed the DHL campaign, which redirects victims to the legitimate DHL site after credential theft.
- The DHL kit gathers device and geolocation details before transmitting data to an attacker-controlled mailbox.
A New Generation of Phishing Kits
A sophisticated phishing kit named Bluekit has emerged, offering more than 40 templates that mimic popular online services and incorporating an AI Assistant to help cybercriminals draft convincing emails. The kit targets email accounts including Outlook, Hotmail, Gmail, Yahoo, and ProtonMail, as well as cloud services like iCloud, developer platforms such as GitHub, and cryptocurrency services including Ledger. Its unified interface allows operators to select domains, templates, and modes, configure phishing page behavior, and monitor victim sessions in real time. The AI Assistant panel supports multiple large language models, including Llama, GPT-4.1, Claude, Gemini, and DeepSeek, enabling attackers to generate phishing email drafts automatically. This integration reflects a broader trend of cybercrime platforms adopting artificial intelligence to streamline and scale their operations. Earlier this year, on ATHR, a voice phishing platform that leverages AI agents for social engineering attacks.
AI Assistant Still in Early Stages
Cybersecurity company Varonis analyzed a limited version of Bluekit's AI Assistant and found that the generated outputs contained placeholder content, suggesting the feature is still experimental. “The draft included a useful structure, but it still depended on generic link fields, placeholder QR blocks, and copy that would need cleanup before use,” Varonis stated. “Bluekit’s AI Assistant looked more like a way to generate a campaign skeleton than a finished phishing flow.” Despite these limitations, the kit is under active development, receiving frequent updates that could quickly improve its capabilities. Varonis noted that Bluekit is another example of an “all-in-one” phishing platform, giving lower-tier cybercriminals access to fully fledged tools that manage the entire attack lifecycle, from domain registration to data exfiltration.
Granular Control and Real-Time Monitoring
Bluekit provides operators with granular control over phishing page behavior, including the ability to block VPN or proxy traffic, headless user agents, and set fingerprint-based filters. The dashboard allows users to configure redirects, anti-analysis mechanisms, and login process handling. Stolen credentials and session data are exfiltrated via Telegram private channels, ensuring that only the kit operators can access the harvested information. Varonis reviewed templates for iCloud, Apple ID, Gmail, Outlook, Hotmail, Yahoo, ProtonMail, GitHub, Twitter, Zoho, Zara, and Ledger, noting that each template features realistic designs and logos. The kit's unified interface simplifies the process of setting up a phishing campaign, making it accessible even to less technically skilled attackers.
DHL-Themed Campaign Targets Global Users
Separately, a phishing campaign masquerading as DHL is actively targeting consumers worldwide, using a fake one-time password page and a branded login portal to steal credentials. The attack chain begins with a spoofed email that lures victims to a counterfeit OTP page, which captures the victim's email address and gathers device and geolocation details. Victims are then redirected to a credential-harvesting web portal, and after data exfiltration, they are sent to the legitimate DHL website to reduce suspicion. Forcepoint X-Labs examined the phishing email, malicious links, and JavaScript responsible for generating a client-side OTP. Their analysis revealed that the kit exfiltrates captured data through EmailJS, a legitimate email service, making detection more difficult. Researchers were able to reproduce the full attack flow in a sandbox environment, confirming the effectiveness of the lightweight infrastructure.
Defensive Measures and Recommendations
Security teams are advised to block suspicious sender domains and watch for DKIM alignment mismatches that may indicate spoofing. Filtering or blocking URLs resolving to identified malicious domains can prevent initial access, while monitoring for unexpected EmailJS activity with unusual payloads can help surface credential theft attempts. Enforcing multi-factor authentication on DHL-related accounts adds an additional layer of protection. Defenders should notify targeted users about the phishing campaign and require password resets for any compromised accounts. The malicious email should be quarantined, and related domains blocked at the email and web gateway layers. Detection rules should be updated to identify the observed URL patterns and the EmailJS-based exfiltration method. The DHL campaign's use of a legitimate service like EmailJS underscores the evolving sophistication of phishing operations.
The Growing Threat of AI-Enabled Phishing
The emergence of Bluekit and similar platforms highlights a significant shift in the cybercrime landscape, where artificial intelligence is being harnessed to automate and enhance phishing attacks. While Bluekit's AI Assistant is still in its infancy, its potential to generate convincing phishing emails at scale poses a serious threat. The integration of multiple AI models gives attackers flexibility, allowing them to choose the most effective language model for their target audience. As these tools become more accessible, the barrier to entry for cybercriminals lowers, enabling a wider range of actors to conduct sophisticated attacks. The DHL campaign, meanwhile, demonstrates that even lightweight kits can be highly effective when they leverage trusted brands and clever social engineering. Organizations must remain vigilant, updating their defenses to counter both AI-generated content and traditional phishing lures.
Outlook: A Rapidly Evolving Threat Landscape
Bluekit is currently under active development, with frequent updates that suggest it could quickly gain adoption among cybercriminals. Its all-in-one approach simplifies the entire phishing lifecycle, making it a compelling tool for attackers who lack technical expertise. The kit's ability to block VPN traffic and headless browsers indicates a focus on evading security researchers and automated analysis systems. As AI models continue to improve, the quality of generated phishing content is likely to increase, making detection even more challenging. The combination of realistic templates, AI-assisted drafting, and real-time monitoring positions Bluekit as a significant threat in the coming months. Security professionals must stay ahead of these developments by investing in advanced detection technologies and user education.
The bottom line
- Bluekit offers over 40 realistic templates and an AI Assistant that uses multiple language models to draft phishing emails, though the AI feature is still in early development.
- The kit provides granular control over phishing pages, including VPN blocking and fingerprint-based filters, and exfiltrates stolen data via Telegram.
- A separate DHL-themed phishing campaign uses a fake OTP page and EmailJS to steal credentials, redirecting victims to the legitimate DHL site to avoid suspicion.
- Forcepoint X-Labs analyzed the DHL campaign, which gathers device and geolocation data before exfiltration, highlighting the use of lightweight infrastructure.
- Defenders should monitor for EmailJS abuse, enforce MFA on sensitive accounts, and update detection rules to counter both AI-generated and traditional phishing attacks.
- The integration of AI into phishing kits lowers the barrier for cybercriminals and signals a rapidly evolving threat landscape that requires proactive security measures.


Raptors Face Elimination After Barnes and Ingram Injuries in Game 5 Loss to Cavaliers

Maxey and George Power 76ers Past Celtics 106-93, Forcing Game 7

Phoenix Fuel Masters Turn to Jonathan Williams as TNT Clash Looms in PBA Commissioner's Cup
