Copy Fail: New Linux Kernel Flaw Gives Root Access via 732-Byte Python Script
A logic bug in the kernel's cryptographic subsystem allows unprivileged users to corrupt the page cache of any readable file and escalate to root, affecting every major Linux distribution since 2017.

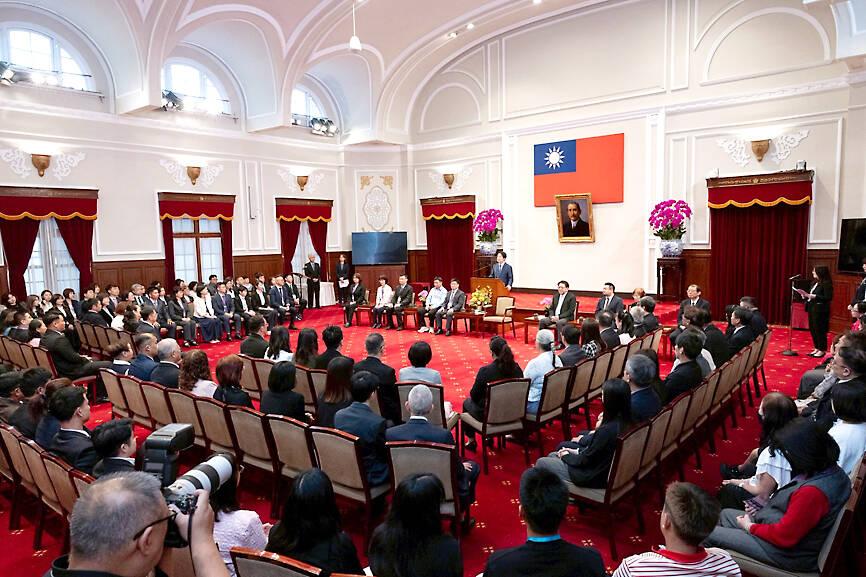
TAIWAN —
Key facts
- CVE-2026-31431 has a CVSS score of 7.8 and is dubbed Copy Fail by researchers at Xint.io and Theori.
- The vulnerability was introduced in a source code commit in August 2017 within the algif_aead module.
- A 732-byte Python script can exploit the flaw to edit a setuid binary and obtain root on any vulnerable Linux distribution.
- The exploit requires no race condition or kernel offset, making it reliably triggerable across all affected systems.
- Patches were released in kernel versions 7.0, 6.19.12, 6.18.12, 6.12.85, 6.6.137, 6.1.170, 5.15.204, and 5.10.254.
- Few Linux distributions had incorporated the fixes when the exploit code was made public on Wednesday evening.
- The flaw enables cross-container compromise because the page cache is shared across all processes on a system.
A Single Script Grants Root on Nearly Every Linux System Since 2017
Cybersecurity researchers have disclosed a high-severity local privilege escalation vulnerability in the Linux kernel that allows an unprivileged local user to obtain root access. Tracked as CVE-2026-31431 and codenamed Copy Fail, the flaw carries a CVSS score of 7.8. The vulnerability was uncovered by the research teams at Xint.io and Theori. The exploit is remarkably simple: a 732-byte Python script can corrupt the page cache of any readable file on the system, including setuid binaries, to elevate privileges to root. The script works across all major Linux distributions shipped since 2017, including Amazon Linux, Red Hat Enterprise Linux, SUSE, Ubuntu, and Debian. The researchers demonstrated that the same exploit code functions without modification on Ubuntu 22.04, Amazon Linux 2023, SUSE 15.6, and Debian 12. The attack requires only that an attacker already has some way to execute code on the machine, even as an unprivileged user. From there, the exploit promotes them to root, granting the ability to read every file, install backdoors, monitor all processes, and pivot to other systems.
A Logic Flaw in the Kernel's Crypto Subsystem
At its core, the vulnerability stems from a logic flaw in the Linux kernel's cryptographic subsystem, specifically within the algif_aead module. The issue was introduced in a source code commit made in August 2017. The flaw lies in the authencesn AEAD template, which IPsec uses for Extended Sequence Number support. Theori explained that the kernel places page cache pages in a writable scatterlist, and authencesn uses the caller's destination scatterlist as scratch space. A 2017 optimization put page cache pages into that writable scatterlist. When performing byte rearrangement in the scratch space, authencesn makes a call that writes four bytes of code past the AEAD tag, into the cached copy of another file. "The 'copy' of the AAD ESN bytes 'fails' to stay inside the destination buffer," Theori stated. The result is that an unprivileged local user can write four controlled bytes into the page cache of any readable file on a Linux system and use that to gain root.
Exploitation Steps and Cross-Container Impact
The Python exploit involves four steps: opening an AF_ALG socket and binding to authencesn(hmac(sha256),cbc(aes)); constructing the shellcode payload; triggering the write operation to the kernel's cached copy of "/usr/bin/su"; and calling execve("/usr/bin/su") to load the injected shellcode and run it as root. What makes this vulnerability particularly dangerous is that it can be reliably triggered and does not require any race condition or kernel offset. On top of that, the same exploit works across distributions. "Reliability isn't probabilistic, and the same script works across distributions," researchers from Bugcrowd wrote. "No race window, no kernel offset." The vulnerability also has cross-container impacts because the page cache is shared across all processes on a system. This means an attacker in one container can compromise the host node and other tenants. The main threat, Theori says, is that all changes are made directly in memory, and the file on disk remains unmodified.
Disclosure Timeline and Patch Gap
Theori privately disclosed the vulnerability to the Linux kernel security team five weeks before releasing the exploit code publicly on Wednesday evening. The kernel team patched the vulnerability in versions 7.0, 6.19.12, 6.18.12, 6.12.85, 6.6.137, 6.1.170, 5.15.204, and 5.10.254. However, few Linux distributions had incorporated those fixes at the time the exploit was released. Distributions known to have patched the vulnerability include Arch Linux and Red Hat Fedora. Others had released only mitigation guidance. The disclosure has drawn criticism from security experts. Will Dormann, a senior principal vulnerability analyst at Tharros Labs, said in an interview: "The org doing the disclosure… did an absolutely terrible job of vulnerability coordination. What is mind boggling to me is that in their writeup they both: A) list 4 affected vendors, and B) tell readers to apply vendor patches. But before firing away with the publication, they didn’t bother to see if ANY of the vendors that they list ACTUALLY HAVE PATCHES. (None do)." Attempts to contact Theori representatives were not successful. With the exploit available before fixed distributions were available, the disclosure amounts to something very similar to a zero-day vulnerability being dropped, although the stiffer term is probably "zero-day patch gap."
Comparison with Dirty Pipe and Dirty Cow
Copy Fail belongs to the same class of vulnerability as Dirty Pipe (CVE-2022-0847) and Dirty Cow (CVE-2016-5195), both of which were actively exploited in the wild. Dirty Pipe allowed unprivileged users to splice data into the page cache of read-only files and ultimately overwrite sensitive files to achieve code execution. Dirty Cow exploited a race condition in the copy-on-write path. "Copy Fail is the same class of primitive, in a different subsystem," said David Brumley of Bugcrowd. "The 2017 in-place optimization in algif_aead allows a page-cache page to end up in the kernel’s writable destination scatterlist for an AEAD operation submitted over an AF_ALG socket. An unprivileged process can then drive splice into that socket and complete a small, targeted write into the page cache of a file it doesn't own." Unlike Dirty Pipe and Dirty Cow, Copy Fail exploits a straight-line logic flaw, making it more reliable. The patches rolled out for Copy Fail remove the optimization introduced in 2017, reverting to out-of-place operation and removing the mechanism that "linked page cache tag pages into the writable destination scatterlist," Theori noted.
Urgent Advice for Organizations
Organizations are advised to update their Linux distributions to a fixed version as soon as possible, especially in environments running untrusted workloads. The vulnerability poses a high risk for multi-tenant Linux environments, as well as for shared-kernel containers and CI runners executing untrusted code. An attacker could, among other things, hack multi-tenant systems, break out of containers based on Kubernetes or other frameworks, and create malicious pull requests that pipe the exploit code through CI/CD workflows. Linux distributors frequently stick with older kernel versions and backport fixes into them. There’s no indication in the disclosure deadline that Theori ever contacted the distributors. Security experts have echoed the perspective that Copy Fail poses a serious threat, with one saying it’s the "worst make-me-root vulnerabilities in the kernel in recent times." The vulnerability is not remotely exploitable in isolation, but a local unprivileged user can get root simply by corrupting the page cache of a setuid binary. The same primitive also has cross-container impacts as the page cache is shared across all processes on a system.
The bottom line
- Copy Fail (CVE-2026-31431) is a Linux kernel local privilege escalation flaw that gives root access via a 732-byte Python script affecting all major distributions since 2017.
- The vulnerability is a logic bug in the algif_aead module, introduced in August 2017, that allows writing four controlled bytes into the page cache of any readable file.
- The exploit requires no race condition or kernel offset, making it reliably triggerable across all vulnerable systems.
- Patches are available in kernel versions 7.0, 6.19.12, 6.18.12, 6.12.85, 6.6.137, 6.1.170, 5.15.204, and 5.10.254, but few distributions had applied them when exploit code was released.
- The flaw enables cross-container compromise because the page cache is shared across all processes on a system.
- Organizations should urgently update their Linux distributions, especially in multi-tenant and container environments.






IBM and Dallara Train AI to Simulate Race Car Aerodynamics in Seconds, Cutting CFD from Thousands of Hours

統一超砸20.54億入股日本LOPIA台灣事業,取得零售超市51%股權

Sony Confirms One-Time Online Check for Digital PlayStation Games After 30-Day Timer Sparks Outcry